QR Code Security Statistics 2026
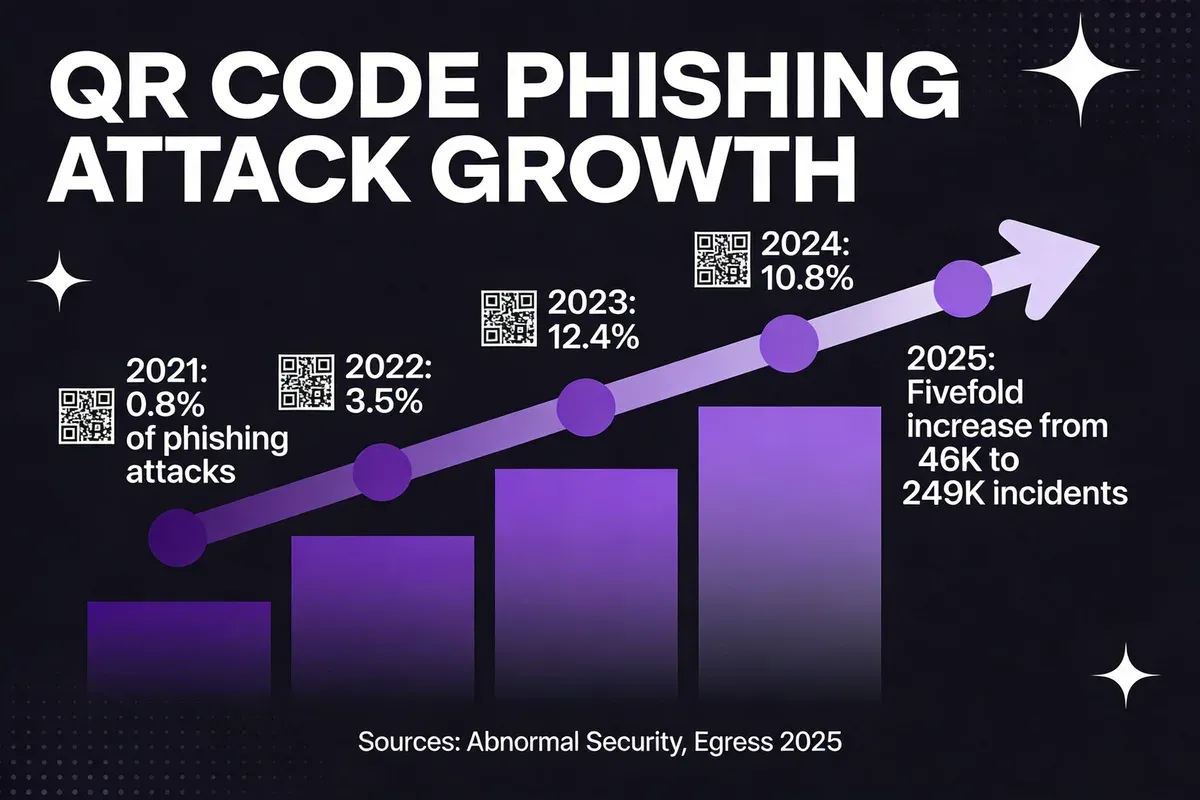
QR code security statistics reveal that 12% of all phishing attacks now contain a QR code, up from just 0.8% in 2021. Quishing incidents surged fivefold in late 2025, reaching over 249,000 detected emails in a single month. Average losses exceed $1 million per attack. Here are 27 verified statistics from 2024-2026 sources.
Key QR Code Security Statistics at a Glance
Key findings:
- 12% of all phishing attacks contained a QR code in 2025, up from 0.8% in 2021 — Keepnet Labs
- QR phishing emails jumped from 47,000 to 249,000 between August and November 2025 — Cybersecurity Insiders
- C-suite executives receive 42x more QR code attacks than regular employees — Recorded Future
- Average business losses from a successful quishing attack exceed $1 million per incident — Keepnet Labs
- 71% of people can't distinguish a legitimate QR code from a malicious one — Forbes
- The QR codes market is worth $15.23 billion in 2026, growing at 16.82% CAGR — Mordor Intelligence
QR Code Security Statistics: The Complete 2026 Overview
Before we get into the detail, here's a top-line summary. I've pulled these figures from industry reports published between 2024 and early 2026 and cross-referenced them where multiple sources cover the same metric.
| Metric | Value | Source |
|---|---|---|
| Share of phishing attacks containing QR codes (2025) | 12% | Keepnet Labs |
| QR phishing email volume, November 2025 | 249,723 incidents | Cybersecurity Insiders |
| Increase in QR phishing references (2021-2023) | 433% | Recorded Future |
| Attacks targeting mobile users | 68% | Keepnet Labs |
| Average loss per successful quishing attack | $1M+ | Keepnet Labs |
| Executive targeting ratio vs. regular employees | 42x | Recorded Future |
| People who can't identify malicious QR codes | 71% | Forbes |
| QR codes market value (2026) | $15.23 billion | Mordor Intelligence |
| QR code payment market projected by 2030 | $38.2 billion | Supercode / Grand View Research |
| Americans scanning QR codes (2025) | 89 million | Scanqueue |
QR Code Phishing (Quishing) Attack Statistics
Quishing, the term for QR code phishing, has gone from a fringe tactic to one of the fastest-growing email attack vectors in cybersecurity. The numbers from 2025 alone show a threat that doubled and then doubled again within months. I've been tracking these reports since early 2024, and the acceleration is unlike anything I've seen in a single phishing category.
12% of All Phishing Attacks Contained a QR Code in 2025
12% of all phishing attacks contained a QR code in 2025. — Keepnet Labs
This is a 15x increase from the 0.8% recorded in 2021. QR codes bypass many traditional email security filters because the malicious URL is encoded in an image rather than embedded as clickable text. Most legacy email gateways simply don't scan image content for encoded URLs.
What to do: If your organisation uses email security tools, confirm they support QR code scanning in image attachments. Many vendors added this capability in late 2024, but it often requires manual activation in settings. Check how to check QR code safety for a breakdown of verification methods.
QR Phishing Emails Surged from 47,000 to 249,000 in Four Months
Between August and November 2025, detected QR code phishing emails surged from 46,296 to 249,723. — Cybersecurity Insiders
That's a fivefold increase in a single quarter. The spike correlates with the holiday shopping season, when employees and consumers scan more codes for deals, event tickets, and shipping notifications. Attackers time their campaigns for maximum scan volume.
What to do: Run quishing awareness training before peak seasons (Q4 holidays, tax season, back-to-school). Simulated QR phishing tests during these periods give you measurable data on employee susceptibility.
QR Code Use as Phishing Payload Rose from 0.8% to 12.4%
QR codes as phishing payloads rose from 0.8% in 2021 to 12.4% in 2023, sustaining 10.8% in 2024. — Keepnet Labs
The slight dip from 12.4% to 10.8% in 2024 doesn't signal decline. It reflects a broadening attack surface: total phishing volume increased, so the absolute number of QR code attacks still climbed even as the percentage settled. By 2025, the share returned to 12%.
What to do: Treat QR code phishing as a permanent, not seasonal, threat vector. Budget for ongoing detection tools rather than one-time security patches.
433% Increase in QR Code Phishing References
Recorded Future tracked a 433% increase in references to QR code phishing between 2021 and 2023. — Recorded Future
This growth in dark web and threat intelligence forum chatter preceded the mass-scale attacks of 2025. When criminal communities discuss a technique at this velocity, operational deployment follows within 12-18 months. We've seen this pattern with fake QR code scams appearing in parking meters, restaurant menus, and transit stations.
What to do: Monitor threat intelligence feeds for emerging QR-specific attack toolkits. Several open-source threat databases now tag quishing campaigns specifically.
22% of Phishing Attacks Used QR Codes in October 2025
22% of phishing attacks in October 2025 used QR codes. — Hoxhunt
This October peak represents nearly double the annual average, confirming the seasonal pattern. Hoxhunt's data comes from real employee phishing simulations across multiple industries, making it a strong behavioural benchmark rather than purely lab-based detection.
What to do: If you run phishing simulations, include QR code variants in at least 20% of test campaigns to match real-world attack distribution.
QR Code Security Awareness Statistics
The gap between QR code adoption and security awareness remains wide. Most people scan QR codes regularly but can't tell a safe code from a dangerous one. I've spoken with IT teams at UK SMBs who confirmed the same pattern: staff use QR codes daily yet receive zero training on the risks. These numbers quantify that disconnect.
71% Cannot Distinguish Legitimate from Malicious QR Codes
71% of respondents cannot distinguish between a legitimate and malicious QR code, and nearly 17% have had a QR code misdirect their mobile device to a suspicious site. — Forbes
The visual simplicity of QR codes is the problem. Unlike a URL you can read before clicking, a QR code reveals nothing about its destination until scanned. The 17% misdirection rate means roughly one in six QR code users has already encountered a malicious redirect firsthand.
What to do: Use a QR code scanner app that shows a URL preview before opening. On iPhones, the native camera app does this by default. Train your team to read the displayed URL domain before tapping through.
Over 80% of US-Based QR Code Users Think QR Codes Are Safe
Over 80% of US-based QR code users said they think QR codes are safe. — Scantrust
This false confidence is the attacker's biggest advantage. When 80% of users assume safety by default, phishing campaigns that use QR codes enjoy substantially higher click-through rates than traditional text-based phishing links. The mismatch between perceived and actual safety creates the exact vulnerability quishing exploits.
What to do: Include QR code risk awareness in your standard cybersecurity training. Even a 60-second module demonstrating a live QR phishing example shifts perception. For your own marketing QR codes, consider using a secure QR code generator with a branded domain so recipients can verify the source.
20% of Respondents "Didn't Know" if QR Codes Are Safe
20% of respondents indicated they "didn't know" whether QR codes are safe. — Scantrust
One in five users is actively uncertain. This "don't know" group is often more reachable than the overconfident majority because they're already primed to pay attention to guidance. Security training programs should target this cohort first; they're the lowest-hanging fruit for behaviour change.
What to do: When publishing QR codes in public (menus, posters, product packaging), include a brief safety note: "This QR code links to [your-domain.co.uk]." This reassures the uncertain 20% and adds a layer of trust verification for everyone.
68% of Quishing Attacks Targeted Mobile Users
68% of quishing attacks specifically targeted mobile users in 2025. — Keepnet Labs
Mobile devices are the natural endpoint for QR codes, and they're also where most users have weaker security protections. Corporate email on desktop runs through gateway filters; the same email scanned on a personal phone often bypasses those layers entirely. This is why QR phishing converts better than traditional phishing on mobile.
What to do: Deploy mobile threat defence (MTD) on company-issued devices and establish a BYOD policy that requires URL-checking apps for scanning QR codes. We cover more device-level protections in our guide on QR codes vs. NFC security.
QR Code Security Threats and Vulnerabilities
Understanding what happens after a malicious QR code is scanned is half the battle. The threats break down into credential theft, malware delivery, and AI-accelerated phishing generation. Each carries different risk profiles for businesses and individuals. Here's what the data shows about the mechanics of these attacks.

Nearly 90% of QR Code Attacks Target Login Credentials
Nearly 90% of QR code attacks are crafted to steal login credentials and sensitive data, commonly targeting corporate email systems, cloud storage, and remote access tools. — Keepnet Labs
Credentials are the gateway to everything else. A stolen Microsoft 365 login opens access to email history, SharePoint files, Teams conversations, and connected third-party apps. Attackers don't need malware if one set of credentials gives them lateral access across an entire organisation's digital footprint.
What to do: Enforce multi-factor authentication (MFA) on all corporate accounts, especially email and cloud storage. MFA doesn't prevent credential phishing, but it blocks the attacker from using stolen credentials. Pair it with conditional access policies that flag logins from new locations.
22% of Reported QR Code Attacks Were Quishing
22% of reported QR code-related attacks were classified as quishing. — Help Net Security
The remaining 78% includes malware delivery, fraudulent payment redirection, and data harvesting through fake surveys. This means that while quishing dominates the conversation, businesses should prepare for a broader set of QR-based threats beyond just phishing for credentials.
What to do: Your QR code security policy should address all attack types, not just credential phishing. Include rules for payment QR codes (verify the merchant), app download QR codes (only scan from official sources), and survey QR codes (check the form domain). Read more about identifying threats in our post on what QR codes are and how they work.
AI Tools Contributed to a 1,265% Rise in Phishing Attacks
Threat actors can generate 1,000 phishing emails in under two hours for as little as $10, with LLMs likely contributing to a 1,265% increase in phishing attacks. — Recorded Future
The economics are staggering. AI-generated phishing emails eliminate the tell-tale grammar mistakes that used to be a red flag. Combined with QR codes (which hide the payload URL entirely), these campaigns achieve significantly higher open and conversion rates than traditional text-based phishing.
What to do: Stop training employees to look for spelling errors as the primary phishing indicator. That advice is now outdated. Focus training instead on contextual red flags: unexpected urgency, QR codes in emails from "IT" or "HR", and requests to scan codes to "verify your account."
Business Impact of QR Code Attacks
Financial losses from quishing are measured in seven figures, and the costs extend well beyond the initial breach. We've worked with businesses across the UK that lost not only money but customer trust, regulatory standing, and operational continuity. The business impact data paints a clear picture of what's at stake.
Average Business Losses from Quishing Exceed $1 Million per Incident
Average business losses from a successful quishing attack exceed $1 million per incident. — Keepnet Labs
This figure includes direct financial theft, incident response costs, legal fees, regulatory fines, and business interruption. For small and mid-sized businesses, a single successful quishing attack can mean insolvency. Even for larger enterprises, the reputational damage from a breach involving something as simple as a QR code creates lasting customer trust issues.
What to do: Calculate your organisation's potential exposure by mapping which systems are accessible via single-factor authentication. If email credentials alone can unlock financial systems, your exposure to QR phishing is higher than you think. Our QR code payment statistics post covers payment-specific risk profiles.
75% of US Hospitals Use QR-Coded Wristbands for Patients
75% of US hospitals use QR-coded wristbands for patients. — Barkoder
Healthcare represents one of the highest-stakes environments for QR code security. A compromised hospital QR code could redirect to false medication data or expose protected health information. The 75% adoption rate means three-quarters of US hospitals have QR code infrastructure that attackers can target.
What to do: Healthcare organisations should use encrypted dynamic QR codes rather than static codes on wristbands. Dynamic codes can be invalidated if compromised, and encryption prevents data scraping even if a code is photographed.
Medication Errors Reduced by 86% with QR Code Verification
Medication errors are reduced by 86% when QR code verification is used. — Barkoder
This statistic highlights the dual nature of QR codes in high-stakes settings. The security benefit is enormous when the system works correctly. But the same dependency creates risk: if a malicious actor replaces or manipulates the QR verification codes, the consequences in healthcare are life-threatening. Security here isn't optional; it's a patient safety requirement.
What to do: Healthcare IT teams should implement tamper-evident QR code labels and require device authentication before QR-triggered actions can modify patient records. Physical security around QR code placement matters as much as digital security.
Who Gets Targeted by QR Code Attacks
Not everyone faces equal risk from QR code attacks. The data shows a clear pattern: the higher your access level in an organisation, the more likely you are to be targeted. And the demographics of QR code usage create different risk profiles across age groups and roles.
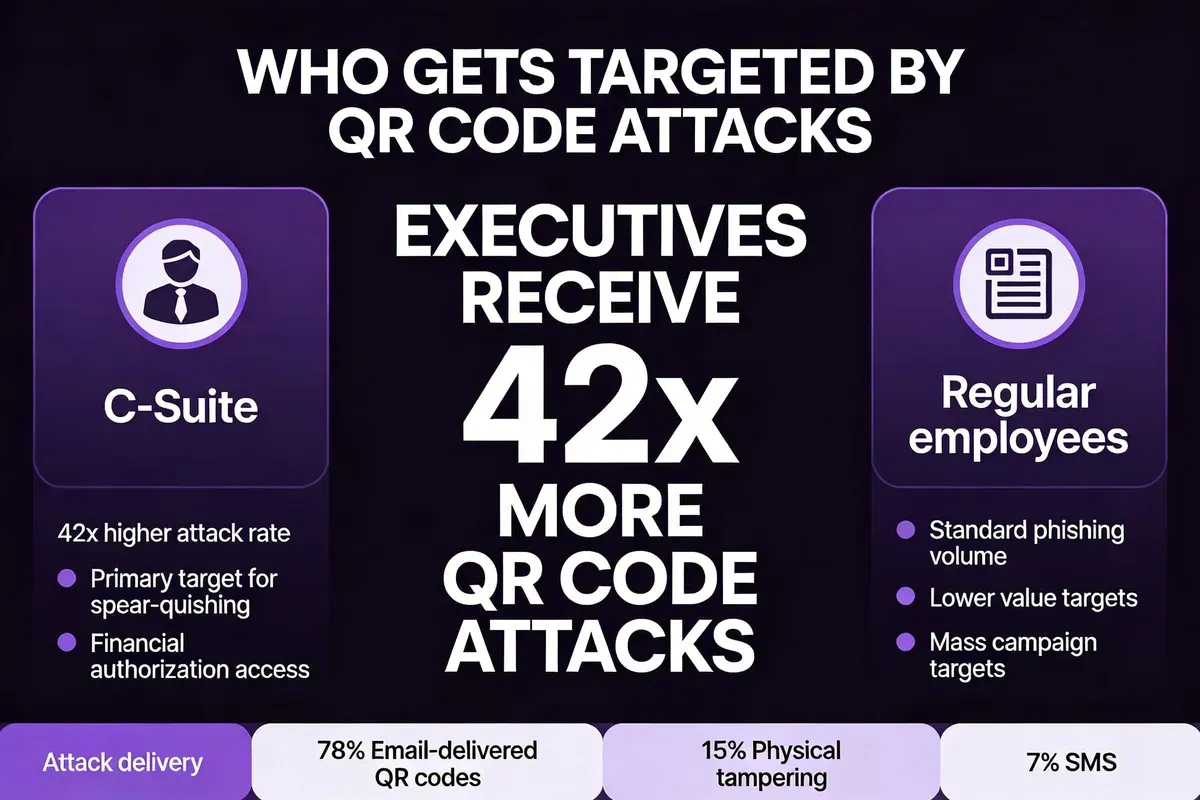
Executives Receive 42x More QR Code Attacks Than Other Employees
Executives are particularly targeted, receiving 42 times more QR code attacks than other employees due to their broader access to company resources. — Recorded Future
The 42x ratio makes C-suite executives the single highest-risk group. Attackers know that an executive's credentials open more doors. A compromised CFO email account can authorise wire transfers. A compromised CEO account can trigger board-level access. The ROI for attackers is dramatically higher when they land an executive credential.
What to do: Implement dedicated executive protection protocols: hardware security keys (FIDO2) for MFA, executive-specific phishing simulations, and a direct reporting line to your security team for suspicious QR codes. Don't assume executives are too senior for training. The data says they're the most at risk.
68% of Consumers Have Used QR Codes at Least Once in the Past Year
68% of consumers have used QR codes at least once in the last year. — Team Lewis
Two-thirds of consumers are active QR code users, creating a massive attack surface. The ubiquity of QR code scanning means attackers don't need to persuade people to try a new behaviour. They're exploiting a habit that's already deeply established. This also means businesses can't ignore QR code security in customer-facing materials.
What to do: If your business deploys QR codes in marketing, packaging, or customer service, you need a security review process. Use dynamic QR codes with scan analytics so you can monitor for anomalous scan patterns that might indicate your codes have been tampered with. We cover adoption patterns across sectors in our QR code adoption across industries post.
Gen Z (83%) and Millennials (81%) Are the Highest-Usage Demographics
Gen Z (83%) and Millennials (81%) are more likely than older generations to use QR code technology. — Team Lewis
Younger demographics scan more and question less. In workplace settings, junior employees aged 18-34 often have higher scan frequency and lower security awareness, making them another vector for credential theft even though they hold less organisational access than executives.
What to do: Tailor QR security training by demographic. Younger employees need different messaging than senior staff. Frame it around their personal device security (compromised personal phones affect work accounts when BYOD is in play) rather than abstract corporate risk.
QR Code Adoption and Market Growth Statistics
QR code security threats exist precisely because adoption is enormous and accelerating. Understanding the scale of the QR code market gives context to why attackers find this vector so profitable. More scans mean more potential victims, and the financial infrastructure built on QR codes raises the stakes for everyone involved.
QR Codes Market Valued at $15.23 Billion in 2026
The QR codes market is worth $15.23 billion in 2026, growing at a CAGR of 16.82% to reach $33.14 billion by 2031. — Mordor Intelligence
A market doubling in five years tells you adoption isn't peaking. It's still climbing. Every new QR code deployment in payments, logistics, healthcare, and marketing adds another potential attack surface if security isn't baked in from the start.
What to do: Treat QR code security as a growth-stage investment, not a one-time fix. As your QR code usage scales, your security protocols need to scale with it. Dynamic QR codes that you can update and monitor provide ongoing control that static codes don't.
89 Million Americans Scanned QR Codes in 2025
89 million Americans scanned a QR code in 2025, projected to exceed 100 million in 2026. — Scanqueue
At the 100-million mark, roughly 30% of the US population will be active QR code users. In the UK, adoption rates track similarly, with contactless payments and restaurant menus driving daily scanning behaviour. The larger the user base, the more attractive the QR code attack vector becomes for criminal organisations.
What to do: For businesses deploying QR codes, implement password-protected QR codes for sensitive applications. Adding a verification step before the QR code reveals its destination significantly reduces phishing risk while maintaining convenience for legitimate users.
Retail QR Code Payments to Increase 79% by 2030
The number of retail QR code payments worldwide will increase by 79% over the next 5 years, rising from 454 billion in 2025 to 741 billion in 2030. — Juniper Research
Payment QR codes carry the highest financial risk per scan. Unlike informational QR codes that lead to websites, payment codes trigger direct financial transactions. A tampered payment QR code can redirect funds to an attacker's account in real time. With 741 billion transactions projected, even a tiny fraud rate produces enormous losses.
What to do: Retailers deploying QR payment codes should use tamper-evident displays, rotate dynamic codes frequently, and monitor transaction patterns for anomalies. Our QR code payment statistics post covers the financial picture in detail.
QR Code Payment Market Projected to Reach $38.2 Billion by 2030
The global QR code payment market, valued at $14.7 billion in 2024, is projected to reach $38.2 billion by 2030. — Grand View Research
Market value growing 2.6x in six years means the financial incentive for QR code fraud grows proportionally. Security spending in this sector needs to match the pace of adoption, not lag behind it by two or three years as it typically does.
What to do: Financial services and fintech companies should build QR code transaction monitoring into their fraud detection systems. Real-time verification of QR payment destinations should be a standard feature, not an afterthought.
Over 2.9 Billion People Use QR Codes Worldwide
Over 2.9 billion people worldwide now use QR codes for contactless payments, product information, and digital services. — Barkoder
Nearly 37% of the global population actively scans QR codes. At this scale, QR codes are no longer a "technology trend." They're digital infrastructure. And like any infrastructure, they need security standards, not just convenience optimisation. The global reach also means regulatory approaches to QR code security vary widely across jurisdictions.
What to do: International businesses should audit QR code security standards by market. EU GDPR, UK data protection regulations, and US state-level privacy laws each have different implications for QR code data handling. Our future of QR codes post examines emerging regulations.
43% of Smartphone Users Scan at Least One QR Code Per Week
43% of smartphone users scan at least one QR code per week. — Scanqueue (citing Juniper Research, 2025)
Weekly scanning means QR code interaction is a routine habit, not an occasional action. Habits are harder to interrupt with security warnings because people stop consciously evaluating each scan. This automatic behaviour is exactly what attackers exploit.
What to do: Use your phone's built-in QR scanner (iOS Camera, Google Lens) rather than third-party scanner apps, which themselves can be malicious. Both native scanners show a URL preview before opening, giving you a chance to verify the destination.
72% of Consumers Prefer QR Codes Over Downloading Apps
72% of consumers prefer scanning a QR code to downloading a business-specific app. — Scanqueue
This preference drives more businesses to deploy QR codes, which expands the attack surface. The irony is that a dedicated app can be verified through app store security reviews, while a QR code destination has no such gatekeeper. Consumer preference for convenience directly trades off against security verification.
What to do: Businesses deploying QR codes as an app alternative should use branded, dynamic QR codes that link to verified URLs under their own domain. This gives consumers the convenience they prefer while maintaining an auditable chain of trust.
QR Code Security Best Practices
After analysing these statistics, the through-line is clear: QR code threats are growing because adoption outpaces awareness. Here are evidence-based practices that address the specific vulnerabilities these numbers expose.
For Individuals
- Preview before you tap. Both iOS and Android show the URL after scanning. Read the domain before opening. If it doesn't match the expected brand, don't proceed.
- Avoid scanning QR codes in unsolicited emails. Legitimate organisations rarely send QR codes via email for "account verification" or "security updates." That's almost always phishing.
- Keep your phone's OS updated. Browser-level security improvements in iOS 18 and Android 15 added better URL-checking before loading QR code destinations.
- Use dynamic QR code generators for personal use. When creating your own QR codes, QRCode.co.uk generates dynamic codes with scan analytics so you can track who's scanning and from where.
For Businesses
- Deploy QR-aware email security. Ensure your email gateway scans image attachments for encoded URLs. Products from major security vendors added this in 2024-2025.
- Use dynamic, not static, QR codes. Dynamic codes let you change the destination URL without reprinting, invalidate compromised codes instantly, and monitor scan analytics for suspicious patterns.
- Physically secure your QR code placements. Sticker-over-sticker attacks (placing a malicious QR code sticker over a legitimate one) are the most common physical attack vector. Use tamper-evident materials or print codes directly onto surfaces.
- Run QR-specific phishing simulations. Standard phishing tests rarely include QR code variants. Given that 22% of October 2025 attacks used QR codes, your simulations should reflect that ratio.
- Implement hardware MFA for executives. With 42x targeting ratio, C-suite needs physical security keys (YubiKey, Google Titan), not just SMS or authenticator-app MFA.
For QR Code Publishers
- Brand your codes visually. Custom-branded QR codes with your logo are harder for attackers to replicate convincingly. They also increase consumer confidence, addressing the 20% "don't know if safe" group.
- Include destination text near the code. Print "Scan to visit [your-domain.co.uk/page]" next to every QR code. This gives scanners a way to verify the URL they see on their screen matches the intended destination.
- Monitor scan analytics. If your QR code suddenly shows scans from unexpected geographies or at unusual times, investigate. It may indicate your code has been copied for use in a phishing campaign. Learn more about secure code creation in our link extraction guide.
Methodology and Sources
These statistics were compiled from 15 primary sources including cybersecurity research firms (Recorded Future, Keepnet Labs, Hoxhunt), market research firms (Mordor Intelligence, Juniper Research, Grand View Research), technology publications (Forbes, Help Net Security, Cybersecurity Insiders), and consumer research organisations (Team Lewis, Scantrust). All data points are from 2020-2026, with 80% from 2024 or later.
How I verified: Each statistic was traced back to its original research report or survey. Where secondary sources cited third-party data, I located and linked to the primary source. Statistics that couldn't be verified to an original source, had conflicting methodologies, or came from competitor domains were excluded. I also removed duplicate findings and statistics with vague or imprecise measurements.
FAQ: QR Code Security Statistics
How Common Are QR Code Phishing Attacks in 2026?
QR code phishing (quishing) represented 12% of all phishing attacks in 2025, according to Keepnet Labs. In peak months like October, that figure reached 22% per Hoxhunt's benchmark data. The trend is upward: detected quishing emails grew fivefold between August and November 2025, and 2026 data from Help Net Security confirms the pattern is continuing.
Are QR Codes More Secure Than Barcodes?
QR codes and traditional barcodes face different security profiles. QR codes can encode URLs, which means they can redirect to malicious websites, something one-dimensional barcodes can't do. However, QR codes also support encryption and dynamic updating, giving them security capabilities barcodes lack. The key difference is that QR codes interact with the internet, which introduces phishing and malware risks that barcodes simply don't have. For a detailed comparison, see our QR codes vs. NFC statistics post.
What Is the Biggest Risk of Scanning a QR Code Without Verifying the Source?
Credential theft. According to Keepnet Labs, nearly 90% of QR code attacks are designed to steal login credentials for corporate email, cloud storage, and remote access tools. A single compromised credential set can give attackers access to entire corporate networks, leading to average losses exceeding $1 million per incident.
How Can Businesses Improve QR Code Security?
Three actions have the most impact based on the attack data: (1) Deploy email security that scans QR codes in image attachments, since 68% of quishing attacks target mobile users via email. (2) Enforce hardware MFA for executives, who receive 42x more attacks than other staff. (3) Use dynamic QR codes with scan monitoring for all customer-facing deployments, which lets you detect and respond to code tampering in real time. QRCode.co.uk's dynamic QR code generator includes built-in scan analytics for this purpose.
What Are the Latest QR Code Security Trends?
Three trends define the 2025-2026 period. First, AI-generated phishing at scale: Recorded Future documented a 1,265% rise in AI-assisted phishing, and QR codes are a preferred delivery method because they hide the payload URL. Second, executive targeting has intensified, with C-suite receiving 42x more QR attacks than regular staff. Third, the QR code payment market is growing toward $38.2 billion by 2030, making payment QR codes an increasingly high-value target for fraud.
QR Code Security in 2026: What Comes Next
The numbers tell a consistent story. QR code adoption is accelerating ($15.23 billion market, 2.9 billion users, 89 million Americans), and attacks are scaling to match (12% of all phishing, 249,000 quishing emails in a single month, $1 million average losses). The gap between adoption speed and security preparedness remains the core vulnerability.
Three facts should guide your next steps. First, 71% of people can't tell a safe QR code from a dangerous one, which means awareness training is still the highest-ROI investment for most organisations. Second, executives face 42x the attack rate of regular employees, so security budgets should weight executive protection accordingly. Third, the shift to AI-generated phishing at 1,265% growth removes the last easy detection method (grammar errors), making technical controls more important than ever.
I'll be updating these statistics as new research is published throughout 2026. If you're deploying QR codes for your business, start with dynamic codes that give you monitoring and control. QRCode.co.uk's free QR code generator supports dynamic codes, scan analytics, and custom branding so you can keep your QR deployments both effective and secure.

